- 27
Oct - 2018Cloud Platforms, Home Automation, MicroPython
2 min | 10002#Zerynth: ESP32 & Google IoT Core - Part 2: Getting data from Smart Power Outlets
Cloud Platforms, Home Automation, MicroPython | 2 min | 10002
Table of contentShowThis part 2 of the tutorial will allow you to get data from the smart power outlets and send it to the Google Cloud Platform (GCP) throught the Google IoT Core and using an ESP32 programmed with Zerynth (Python). This data is not usually available to the user (directly, you need to use the power outlet application), and it is sent to the company servers.
If you want to check, if your power outlets are compatible for this tutorial, they should have the port
6668opened. To check that:>>> nmap <<ip-address>> -p 6668 [...] Host is up (0.13s latency). PORT STATE SERVICE 6668/tcp open ircIf the answer is as shown above, the port is opened. If you don't have the
nmapapplication and you are on Windows, look at the Nmap Network Scanning tool. On Ubuntu type on a terminalsudo apt-get install nmap.I've already published a tutorial to control the smart power outlets using MicroPython here, but as I said in part 1, MicroPython does not support JSON Web Tokens (JWT) yet, and thus it is not possible to connect to the GCP. I've tried to develop the connection again, but I needed some Elliptic Curve Cryptography. I had a hard work trying it, but I couldn't finish it :(. I need more knowledge about cryptography. Then, I use Zerynth again.
Using Zerynth, I wasn't able to control the devices because I didn't find any AES cryptography class that worked on it. It is possible to adapt the MicroPython version of AES (check here), but for a first try, I needed only the status data, and I didn't want to control the switches. Thus, the
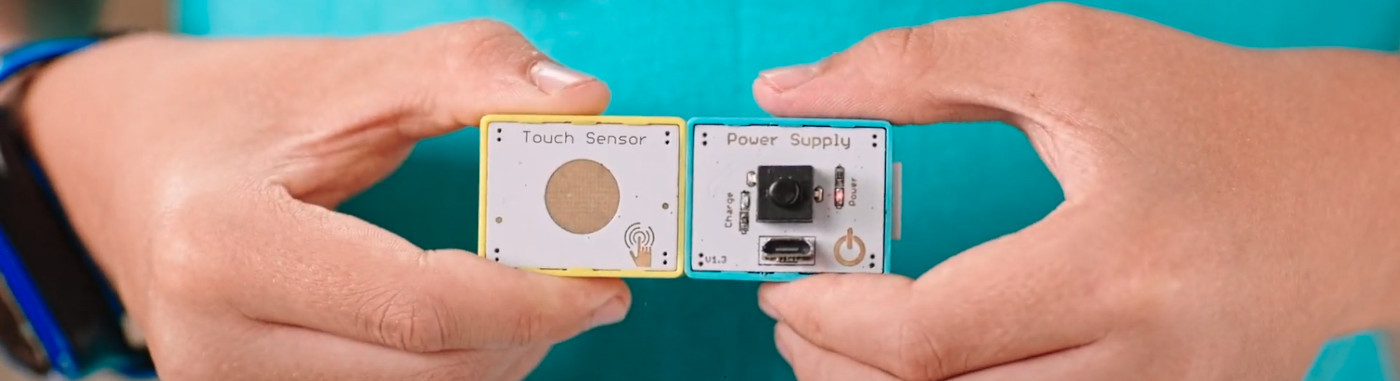
localKeyis not needed. I included the variable on themain.pyfile, but you can leave it blank, or you can write what you want. But you need thedevIdvalue, to get that, check the Key extraction section of this post.Hardware and Software
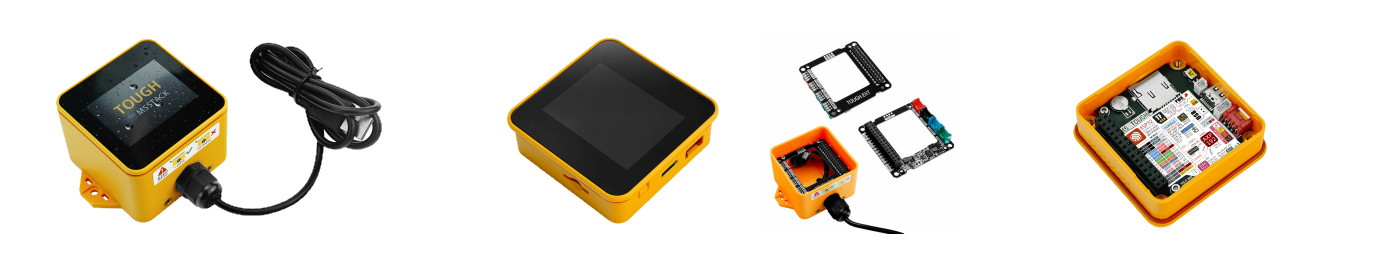
**Important note**: This doesn't work with Sonoff devices, for those you can use Sonoff-Tasmota. This only works with devices known as "Tuya-like" one (Tuya Inc. is the company). Again, if the port 6668 is opened, you have 99.9% chances that this works.DIY
You can program the ESP32 using Zerynth as described on the part 1 of this tutorial. The steps to run this code:
- Clone or download the repository: https://github.com/lemariva/zerynth-smart-outlet
- Configure the:
ssid_: Wi-Fi SSID, where your power outlet is also connected.wp2_pass: WPA2 for the selected Wi-Fi.DEVICE_ID_HERE: use the obtaineddevId. Check here.IP_ADDRESS: IP address of the power outlet on your LAN. You can get that from your Wi-Fi router.LOCAL_KEY: write what you want, or use thelocalKey. Check here.
The following data is available:
a
jsonlike the following (it depends on the power outlet):{ 'dps': { '25': 1165, '24': 17857, '9': 0, '22': 623, '23': 30606, '1': True, '21': 1, '20': 2284, '18': 75, '19': 86 }, 'devId': '80023151840d8e4bbef9' }in my case, the parameter:
1: represents the actual status (True=On, False=Off).18: is the actual mAh consume.19: is the actual W consume.20: is the actual V.
If you have more information about the other parameters, leave me a comment.
Now, I have all the data that I wanted. The next steps are going to be on the GCP to process the data.
We use cookies to improve our services. Read more about how we use cookies and how you can refuse them.




Empty